Using the Windows Active Directory within ScaleArc allows for automatic synchronization of Windows AD user authentication credentials from the AD domain to ScaleArc. These synchronized credentials can then be configured for database user Authentication Offload in the ScaleArc cluster configuration.
You can implement Windows AD in one of two ways:
ScaleArc as RODC
Prerequisites for RODC
Before joining the domain you should have completed the following on ScaleArc:
-
Make sure you have ScaleArc, minimum version 3.10.x installed and running for this configuration.
- ScaleArc recommends you configure the AD DC server as the NTP server in the ScaleArc configuration. The timezones on both the AD DC server and ScaleArc HA pair should also be the same. It is acceptable for the DC and ScaleArc to use the same NTP server, but essential that they are in time synchronization for Windows Authentication to work properly.
- Ensure that the Windows AD domain has been prepped to allow Read-Only Domain Controller (RODC) support. If you have not run
adprep /rodcprepon your forest to allow RODCs to join your domains, run it once for your forest before you attempt to have ScaleArc join a domain in your forest. - Make sure you have observed the maximum length for a hostname recommended by Microsoft for the ScaleArc hostname.
- Verify the primary DNS setting on ScaleArc is correct and ScaleArc is able to ping the AD server by hostname. ScaleArc's primary DNS server should in most cases be the AD DC server; this is the usual setup in AD. If it is not, ScaleArc and the AD domain should use the same DNS server.
- Ensure that DNS forward and reverse lookup are configured correctly for the AD domain and the AD DC on the DNS server that ScaleArc uses.
Optionally, ensure that the Windows AD users who require access to databases serviced by ScaleArc are configured on the desired SQL Server instances. Users can be added to AD and SQL Server after this domain join procedure is complete, and will automatically appear as the user fetch cycle runs; however, pre-configuring some users will allow immediate testing of the ScaleArc AD Integration functionality.
- The time taken to join the domain is directly proportional to the number of objects in the domain. The join takes longer to complete if there is a large number of objects in the domain.
- ScaleArc only authenticates users belonging to the joined domain.
- Joining the domain can be accomplished either before or after configuring HA. ScaleArc recommends you use the latter, that is, joining a linked HA pair to the domain from the HA Primary; this is the easiest method. In this case, both ScaleArc machines are configured; the HA Secondary first and then the HA Primary. If you choose to join the domain before configuring HA, configure Active Directory exactly the same on both ScaleArc machines and then link them in HA. Note that HA linkup will fail if there are any differences in configuration. Refer to the High Availability section for more information on configuring HA in ScaleArc.
- Note that existing Windows domain users defined in the ScaleArc cluster under Users & DBs are NOT overwritten when you configure ScaleArc to integrate with your Windows Active Directory (AD). These users should be manually removed from the ScaleArc Users & DBs before they are reconfigured from the Windows AD domain. If not deleted, the password updates for these users in the AD do not propagate to ScaleArc.
- ScaleArc hostnames that have previously been used with AD Integration should not be re-used; this is particularly true where the host has been taken down and not reactivated for some time. Windows AD has a function called "tombstoning" that can cause problems with re-used hostnames due to AD constraints on change tracking to the AD objects in the domain and this prevents the RODC functionality from working by preventing replication from AD.
Configure for RODC
Before you begin, review these best practices. Then, configure ScaleArc as a Read-only Domain Controler (RODC) as follows:
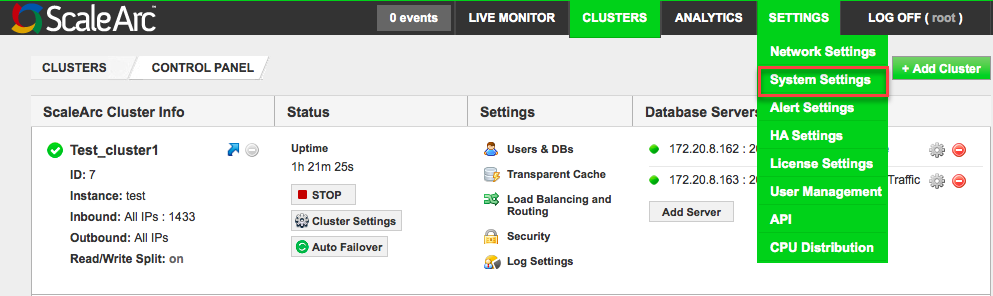
- Click the SETTINGS tab > System Settings on the ScaleArc dashboard.
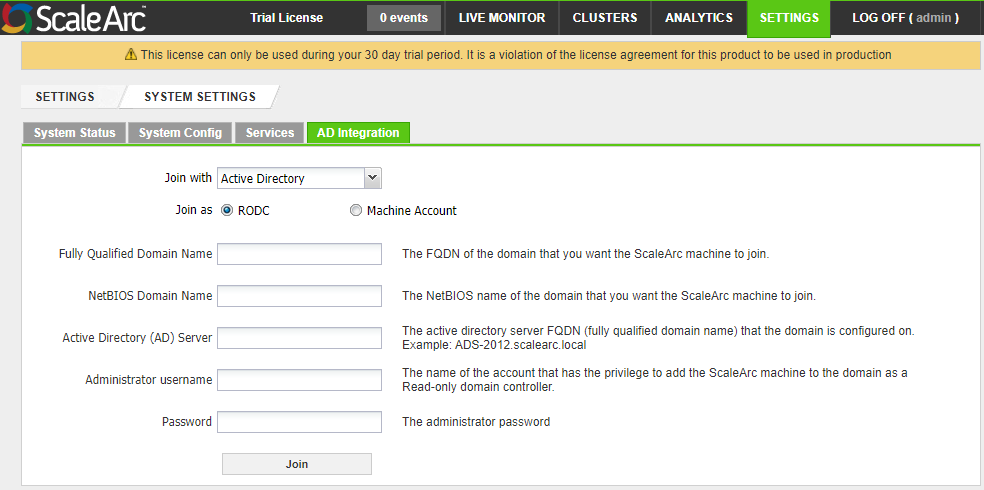
- Click on the AD Integration tab and select AD Integration from the drop-down menu. Select Active Directory from the Join with dropdown.
- Select the RODC radio button.
-
Complete the fields as follows.
Field Description Default/User input Fully Qualified Domain Name (FQDN) Enter the FQDN of the domain that you want the ScaleArc appliance to join.
Enter an appropriate domain name. NetBIOS Domain Name The NetBIOS name of the domain that you want the ScaleArc appliance to join. This is the "short" domain name and ScaleArc automatically enters it correctly.
Enter a NetBIOS name, if necessary. Active Directory (AD) Server
The active directory server FQDN (fully qualified domain name) that the domain is configured on. Note that the server name should not include a trailing dot (".") at the end, unless you are using a valid DNS entry for the name. Enter the FQDN. Administrative username The username of the account that has the privilege to add the ScaleArc appliance to the domain as a Read-only domain controller.
Enter the username. Password The administrator password.
Enter the password. - Click Join the AD Domain to complete the setup. Once connected, you can use Unjoin the AD Domain to leave the domain.
- Add the appropriate domain users and/or groups to the Password Replication Policy for each of the ScaleArc RODC server objects in AD. Note that in an HA configuration this must be done in AD for both ScaleArc RODC objects for the HA pair, or users will not be allowed access after an HA failover operation.
- Add all desired users and groups into the Allowed RODC Password Replication Group for the ScaleArc server in AD.
- The Denied RODC Password Replication Group takes precedence, so membership in this group, or any group that is a member of this group, will prevent the user account from working with ScaleArc AD Integration even if it is allowed by membership in the Allow group. By default, the Deny group contains all the usual administrator groups and administrative users in the domain.
- Refer to this KB article for further information on how to set user replication privileges for the ScaleArc RODC.
- On the SQL Server instances that ScaleArc communicates with, add either user accounts or group accounts to Security > Logins for those users who will access the servers through ScaleArc.
- Go to CLUSTERS > Settings column > Users & DBs.
- Click on the Fetch Users button. By default, Auto Fetch Database Users is OFF. See Auto Fetch for details.
- Turn Auto Fetch Database Users ON. The default for the automatic synchronization interval is 60 seconds. Adjust this value, if required.
- User accounts that are enabled for RODC replication and for SQL Server instance access should appear in the Auto Fetch dialog no later than after two auto fetch intervals.
- You do not have to add the users from the Fetch Users dialog; they can access ScaleArc and the SQL servers if they are in the proper groups in AD and have SQL Server access.
- Note that if you add users from the Fetch Users dialog rather than through AD Integration, those users and their passwords are "frozen." The password in ScaleArc cannot be updated since it is no longer checked in the RODC but is stored in the ScaleArc configuration files. This option supports legacy accounts. To put this another way, any user that appears in the Users & DBs dialog overrides the AD Integration feature and will not be eligible for AD Integration. To update the password for such a user, use the gear icon next to the user account in Users & DBs, not the account in the Fetch Users dialog.
- As noted above in the Prerequisites, this option also applies to pre-existing user accounts in Users & DBs. Such accounts should be deleted from the Users & DBs dialog prior to joining the domain if you require these users to have AD Integration.
- Finally, for ScaleArc's monitoring to work correctly, note that the first account in Users & DBs is not eligible for use with AD Integration. This is the cluster service account, used for health checks and configuration updates.